1. How can it affect my business?
2. What is hacking?
3. How are websites hacked?
4. Is WordPress the only platform affected?
5. How do I know if my website was hacked?
6. What should I do if my website was hacked?
7. How can I avoid being hacked?
How can it affect my business?
The affects of hacking can be devastating for a business (and consumers). Hacks have bankrupt and dissolved businesses. Just take a look at the Mt. Gox (Japan-based Bitcoin exchange) hack from 2011. Initially a hacker identified system credentials and successfully transferred over 2,600 bitcoins to another account. Not long after, they were hit with a second hack where over 750,000 bitcoins were stolen. They were forced to halt operations and file bankruptcy. Customers who had accounts with them lost their funds. Another great example is the data breach at Equifax (read more here).
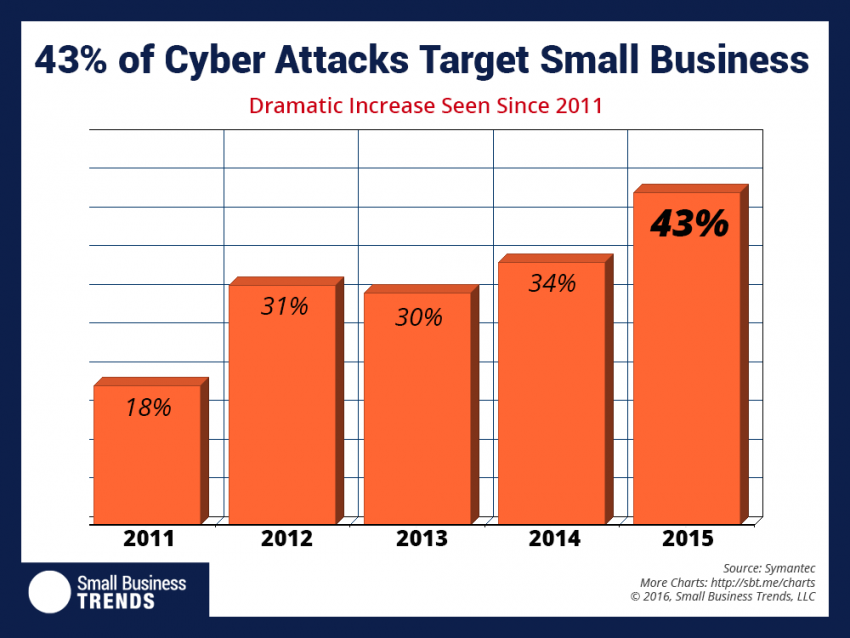
Don’t make the mistake of thinking that just because you are a small business that no one would want to hack your website. According to Symantec’s 2016 Internet Security Threat Report, phishing campaigns targeted small businesses 43% of the time.
Being hacked can destroy your reputation and erode all trust in your business. Imagine being a company that provides some type of security services or is entrusted with sensitive data. A security breach could destroy the business overnight. Malicious code that can be installed on your site from a hack and can cause issues with your organic search rankings. Google, Bing, and other major search engines will recognize the malware and block you from their indexes.
You could even be liable for losses that your customers incur as a result of their credit card numbers or other personal information being stolen due to a breach on your website.
What is hacking?
 You hear people using the terms “Hacking” or “Hacked” quite frequently, especially when it comes to websites. While there are numerous ways that you can actually be hacked, in general terms it is unauthorized access or intrusion into a network. This can be done manually by an individual executing code or unlawfully accessing accounts with known or guessed access credentials. It can also be completely automated. The hacker might suppress the website security or alter the website code in order to accomplish their intended goal.
You hear people using the terms “Hacking” or “Hacked” quite frequently, especially when it comes to websites. While there are numerous ways that you can actually be hacked, in general terms it is unauthorized access or intrusion into a network. This can be done manually by an individual executing code or unlawfully accessing accounts with known or guessed access credentials. It can also be completely automated. The hacker might suppress the website security or alter the website code in order to accomplish their intended goal.
Mirriam Webster defines a hacker as: a person who illegally gains access to and sometimes tampers with information in a computer system.
How are websites hacked?
Hackers can employ a variety of techniques for hacking, some of which include:
- Vulnerability Scanner: Checks for known weaknesses and exploits them. This is why it’s so pertinent for you to quickly upgrade your website software. Once a security issue is identified and a patch is issued, automated hacks will begin on mass scale.
- Key Loggers: These are designed to record keystrokes for later retrieval. They can attempt to parse out access credentials, sensitive personal data, credit card numbers, and anything else they can recognize.
- Brute Force Attack: A brute force attack is when the hacker uses scripts to try various combinations until they figure out your password. This can gain them access to hosting accounts, cpanel, FTP, SSH, etc.
- Password Cracking: Recovering passwords from data stored or transmitted by computer systems.
- Trojan Horse: This is software that serves as a back door in a computer system to allow a hacker to gain access to a system at a time of their choosing. They can do things like install software that takes photos of your payment page and sends the screenshots with card information to their system. Many have had their website files encrypted and have been hijacked until they send ransom money in exchange for what they hope will be the encryption key so they can restore their website.
- Packet Sniffer: These are simple applications that capture data packets so data can be analyzed and information parsed out, similar to the process with analyzing data collected from key loggers.
- Spoofing: This is where email communications and/or websites falsify data by mimicking legitimate sites.
- Viruses: Code that can replicate itself and typically causes damage like deleting, modifying, or corrupting files and/or data.
- SQL Injection Hacks: SQL Injection is when a hacker enters malicious words and characters into a form that is unsecured to exploit the database.
Is WordPress the only platform affected?

WordPress might just me the most widely used Content Management System on the web. According to ManageWP.com, 74,652,825 sites are running on the software. With that large of an audience is (one of) the natural targets for hackers. WordPress (74%), Joomla (17%), and Magento (6%) seem to be among the most hacked CMS platforms. This is based on stats provided by Sucuri (a website security platform) from a sample size of 7,937 compromised websites in the third quarter of 2016. This doesn’t mean that WordPress is necessarily an insecure platform, it means that website owners neglect taking the proper measures and so leave themselves prone.
WordPress is appealing to many developers because it is an open source platform. Open source platforms offer rapid development and robust features to the development community. Unfortunately they are always under close watch by hackers looking for the next way to exploit vulnerabilities of the software for their own gains. Because of this, If you don’t stay up to date with the latest software updates you are going to be vulnerable to a website hack.
How do I know if my website was hacked?
If you don’t regularly browse your website or have software in place that monitors it for you, it probably all started with a customer reporting a strange ad, redirect to a foreign website, or message that their McAfee browser security plugin displayed. There are however a number of indicators and we’ll list some of the most likely ones here.
1. Spam or Malware Links Added to Your Website
One of the most common indicators is data injection. Hackers create a backdoor to modify your WordPress files and database. Usually these hacks add strange links for Viagra prescriptions or redirect you to foreign websites. Deleting the links will not solve the problem. You need to cleanse the malware.
2. Unable to Login to the Admin
No longer able to login to your WordPress admin. You can reset the login directly through MySQL, but until you cleanse the malware the hackers will likely just lock you out again.
3. Sudden Drop in Website Traffic
Many malware and trojan viruses out there that redirect your website’s traffic to other websites. In addition, Google’s safe browsing tool might be showing warnings to users regarding your website and they might remove you from their indexes.
4. Suspicious User Accounts
If you have user accounts because you sell something or have another reason for users to register for accounts on your website and are using spam prevention, then your site was probably hacked. The accounts will typically have administrator roles and you might be unable to delete them.
5. Your Website is Often Slow or Unresponsive
Hackers can install scripts that are running large processes, communicating with third party websites, and might even be using your resources for crypto currency mining. This can cause a major slowdown in the load times on your web pages.
6. Email from Google Search Console
You might get an email from Search Console informing you that your website has been compromised
7. Unknown Files and Scripts on Your Server
If you’re regularly working on your website and are familiar with the file structure and standard WordPress files, you might notice some files which were installed that are out of the ordinary.
8. Your Website Displays Another Website
Some hackers will re-direct your traffic to another website. You would see a new file or a modified existing file with code that looks like this: <meta http-equiv=”refresh” content=”0; url=http://sample.com/” />
9. Message on Homepage
You might see a message that you need to send a payment to an email account in exchange for the decryption key to your website files.
What should I do if my website was hacked?
- If your site’s been hacked, you need to immediately change all of your passwords. We recommend using strong passwords. Change all our your passwords, which might include: cPanel, FTP, databases, and other admin accounts.
- If you are lucky enough to have a recent backup of your website and database (and can determine it was from before you were hacked) restore the backup immediately.
- Use reliable software to remove the malware. You can explore options like Exploit Scanner, Sucuri SiteCheck, or Gravity Scan.
- Then immediately after make sure that you follow the recommendations in the “How Can I Avoid Being Hacked?” section.
How can I avoid being hacked?
Place emphasis on how people access your website, leveraging things like Multi-Factor and Two-Factor Authentication.
Protect yourself against the exploitation of software vulnerabilities through use of a Website Firewall – focus on Known and Unknown Attacks.
Backups are your friends – your safety net – try to have at least 60 days available.
Register your website with Search Engines – Google and Bing have Webmaster Tools, leverage their infrastructure to tell you the health of your website.
- Schedule regular backups. No this will not prevent a hack but in the event that it does happen it will make your life MUCH easier. There are numerous plugins that can do this for you if your hosting plan does not already. UpdraftPlus is one that we happen to like.
- Use strong passwords. It’s tempting to use the name of your poodle, but use long passwords with a variety of upper-case letters, lower-case letters, numbers, and special characters. Make sure your usernames and passwords cannot be guessed.
- Custom WP Admin URL. Change the default WordPress Admin url (http://www.mywebsite.com/wp-admin). Make it a little more difficult and stop some of the automated hacks. There are numerous plugins that can help you do this in minutes.
- Update everything. Don’t wait until you have free time on the weekend, update immediately. If there was a software update that is addressing a security issue that means hackers are already exploiting it. Don’t make yourself an easy target, always update your software.
- Two factor authentication. Install a plugin that sends a security code to your mobile device before allowing you to login. You can look into Google Authenticator.
- Install security software. WordPress has a number of great security plugins. Here are a few that are worth looking into:
Sucuri Security
Wordfence
iThemes Security
Jetpack
BulletProof Security